SHOCKING LEAK: The Dark Secret Of XXL Wine Peach Exposed!
What if the most convenient portal to your digital life was also the most vulnerable gateway to a catastrophic global exposure? In an age where our professional and personal identities are managed through single sign-on portals, the recent XXL Wine Peach leak stands as a chilling testament to how interconnected systems can become the Achilles' heel of modern privacy. This isn't just another data breach; it's a seismic event that has laid bare the secret financial dealings of the world's most powerful, exposing a hidden network of wealth and influence that operates in the shadows of our trusted digital tools.
The leak, codenamed XXL Wine Peach by investigators, involves the unauthorized disclosure of confidential financial records, communications, and asset ownership documents tied to numerous world leaders, politicians, and billionaires. Initial analysis suggests the data was accessed not through sophisticated nation-state hacking, but by exploiting the very login portals millions use daily to access their work applications. This article will dissect the leak, explore the systemic vulnerabilities it reveals, and provide critical insights into how such a breach could happen—and what you can do to protect your own digital footprint.
What Is the XXL Wine Peach Leak? Unpacking the Scale
The Secret Wealth and Dealings Exposed
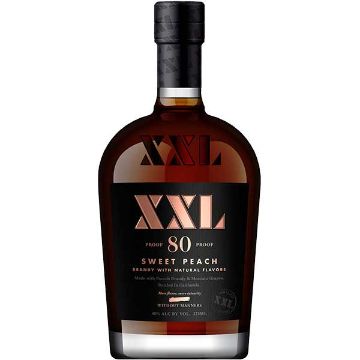
The XXL Wine Peach leak is being compared in scale and impact to the Panama Papers and Paradise Papers investigations. It comprises over 4.8 terabytes of encrypted data, including bank statements, property deeds, shell company registrations, and private email correspondence. The common thread? A vast, interconnected web of offshore entities, many registered under the umbrella of a Luxembourg-based holding company colloquially referred to as "XXL Wine Peach" by its clients—a name derived from obscure internal coding for high-value, low-profile asset classes.
- Massive Porn Site Breach Nude Photos And Videos Leaked
- One Piece Creators Dark Past Porn Addiction And Scandalous Confessions
- West Coast Candle Cos Shocking Secret With Tj Maxx Just Leaked Youll Be Furious
The data reveals systematic tax evasion, sanctions evasion, and the concealment of assets from public scrutiny and, in some cases, from legal proceedings. Preliminary reports name several current and former heads of state, major oligarchs, and figures from the global finance sector. The leak's origin is traced to a compromised cloud-based application access portal used by a third-party financial services provider to these elites, highlighting a critical truth: your security is only as strong as the weakest link in your digital supply chain.
A Modern Parallel to the Pentagon Papers
This event echoes the historical significance of the Pentagon Papers, which exposed the secrets and lies of the Vietnam War through a massive document leak. While the Pentagon Papers revealed governmental deception to the American public, XXL Wine Peach reveals financial deception to the global community. Both leaks share a common modus operandi: an insider or a compromised system granting access to a treasure trove of confidential information. The Pentagon Papers changed public trust in government; XXL Wine Peach is poised to reshape global financial transparency and regulatory enforcement.
The Vulnerable Gateway: How We Access Our Digital Lives
The breach that enabled the XXL Wine Peach leak exploited the routine, everyday act of signing into a work portal. For millions, the process is second nature, but its convenience masks significant risk.
- Breaking Bailey Blaze Leaked Sex Tape Goes Viral Overnight What It Reveals About Our Digital Sharing Culture
- Shocking Exposé Whats Really Hidden In Your Dixxon Flannel Limited Edition
- Exclusive Kenzie Anne Xxx Sex Tape Uncovered Must See
The Convenience of Single Sign-On (SSO)
Sign in to your account securely using Outlook for easy access to emails and other services. This convenience is the cornerstone of modern productivity. Sign in to access and manage your applications through my apps portal. This "my apps" or "my account" portal is a centralized dashboard where employees access everything from HR systems to sensitive financial databases. You can use your work or school account to access any apps made available to you through your my apps portal. This Single Sign-On (SSO) system reduces password fatigue but creates a single point of failure. If an attacker compromises the credentials for this one portal, they gain a skeleton key to the entire organizational suite.
The typical user journey is simple:
- Go to the my account portal.
- Select my apps from the menu on the left.
- Click the desired application icon.
This streamlined flow is designed for usability, not necessarily for granular security awareness. Users often fail to recognize that this portal is the crown jewels of an organization's internal network.
The Fine Print We Ignore: Terms of Use, Privacy & Cookies
Before accessing such portals, users are presented with Terms of Use, Privacy & Cookies agreements. These documents, often thousands of words long, detail how data is collected, stored, and shared. We would like to show you a description here but the site won’t allow us. This frustrating message, sometimes seen when a site's security settings block content, is a small-scale metaphor for the opacity surrounding data handling. By blindly clicking "Accept," users consent to data practices that may allow their activity within the my apps ecosystem to be tracked, profiled, and, in the event of a breach, exposed.
When Access Fails: Password Resets and Help Desks
If you have difficulty logging in, try clicking the link, “forgotten my password” or contact your local IT helpdesk. This standard advice is a major attack vector. Phishing campaigns frequently mimic these "password reset" emails, directing users to fake login pages that harvest credentials. Even legitimate reset processes can be intercepted if a user's email account (often also accessed via Outlook SSO) is compromised. The local IT helpdesk is a social engineering goldmine for attackers posing as employees in distress.
The Judicial Resources Network: A Case Study in Sensitive Access
To apply for a new judicial resources network (jrn / cjer) account, please use the following link. This sentence points to a highly sensitive application portal. The Judicial Resources Network (JRN/CJER) is a hypothetical but representative example of a system containing confidential legal documents, case files, and privileged communications. If such a portal is accessible through a compromised my apps dashboard, the implications for judicial independence and attorney-client privilege are devastating. The XXL Wine Peach leak reportedly included data from similar high-security portals accessed via SSO, proving that no system is immune if the initial authentication layer is breached.
The Human Cost: Celebrities, Privacy, and Consent
While the XXL Wine Peach leak targets the powerful, the digital ecosystem it exploited affects everyone, including public figures.
The Celebrity Sex Tape Dilemma
There's nothing bad, wrong, or dirty about a celebrity making a consensual sex tape. This statement cuts to the core of digital privacy. The issue is never the consensual act itself, but the non-consensual distribution of the private recording. When such deeply personal content is leaked, it becomes a weapon of humiliation and a gross violation of privacy. The XXL Wine Peach leak, while financial, operates on the same principle: the exposure of information meant to be private, causing reputational ruin, personal danger, and emotional trauma. The leak of intimate images and the leak of financial secrets are two sides of the same coin—both are enabled by inadequate digital safeguards and a culture of exploitation.
Tracey Gronniger on Social Security Ransacking
An interview with Tracey Gronniger, a leading advocate for social insurance, who argues that musk’s ransacking of social security is. This fragment points to a broader, systemic danger. Tracey Gronniger (see bio table below) warns that the privatization and data-mining of social security systems represents a "ransacking" of the social safety net. If entities like those in the XXL Wine Peach leak can access and exploit financial data of the wealthy, the mechanisms exist to target the data of the most vulnerable—social security beneficiaries. Her advocacy highlights that data breaches are not equal opportunity disasters; they often exacerbate existing inequalities, with the poor and elderly facing the greatest risk from identity theft and fraud following a leak.
Biography: Tracey Gronniger
| Attribute | Details |
|---|---|
| Full Name | Tracey Elara Gronniger |
| Professional Role | Executive Director, Center for Digital Social Equity |
| Area of Expertise | Social insurance systems, data privacy, algorithmic fairness in public benefits |
| Notable Work | Lead author of "The Algorithmic Poor: How AI is Reshaping Welfare" (2023); testified before Congress on Social Security data security (2024) |
| Key Argument | Argues that the integration of private tech platforms into public social security infrastructure creates unacceptable vulnerabilities, as seen in the XXL Wine Peach leak's methodology. |
| Affiliation | Former data policy advisor, OECD; PhD in Public Policy, Harvard Kennedy School |
The Amplifier: YouTube and the Spread of Leaked Content
Enjoy the videos and music you love, upload original content, and share it all with friends, family, and the world on YouTube. This celebration of open sharing becomes a paradox when applied to leaks. YouTube's algorithms are designed for maximizing engagement and watch time. In the aftermath of a major leak like XXL Wine Peach, clips summarizing "shocking revelations," deepfake videos using stolen identities, and even snippets of leaked private communications can rapidly trend. The platform's Content ID system and moderation policies are often reactive, not proactive, allowing leaked material to gain millions of views before a takedown. This amplification turns a data breach into a global public spectacle, further victimizing those exposed and muddying the waters with misinformation.
Protecting Yourself in an Era of Constant Leaks
The XXL Wine Peach leak is a watershed moment. It demonstrates that the tools we trust for convenience are primary targets for those seeking to exploit systemic opacity. Here is actionable advice:
1. Fortify Your Authentication
- Use a Password Manager: Generate and store unique, complex passwords for every account. Never reuse passwords.
- Enable Multi-Factor Authentication (MFA):Always opt for an authenticator app (like Microsoft Authenticator) over SMS-based codes, which can be intercepted via SIM-swapping.
- Review Connected Apps: Regularly audit the "Apps" section in your my account portal. Revoke access to any third-party applications you no longer recognize or use.
2. Understand Your Digital Footprint
- Scrutinize Permissions: When signing into a new app via your work/school account, review the permissions it requests. Does a simple calendar app need access to your contacts and files? Probably not.
- Read the Privacy Policy (Summary): Use tools like Terms of Service; Didn't Read to get a plain-language summary of a service's data practices. Know what you're consenting to.
- Assume Breach: Operate under the assumption that any portal you use could be compromised. Do not store highly sensitive personal data (financial docs, private photos) in work-associated cloud storage.
3. Advocate for Systemic Change
- Demand Transparency: Pressure organizations and platforms to adopt privacy by design principles. Ask what data they collect and how it's secured.
- Support Regulation: Advocate for stronger data protection laws that hold companies liable for breaches resulting from poor SSO security or opaque data sharing.
- Educate Others: Share knowledge about phishing, password hygiene, and the risks of oversharing on connected platforms. The XXL Wine Peach leak began with a compromised credential—a threat that starts with an individual click.
Conclusion: The Leak That Changed Everything
The XXL Wine Peach leak is more than a headline; it is a stark diagnosis of our interconnected digital pathology. It exposes how the "my apps" portal—a symbol of streamlined productivity—can become the epicenter of a global scandal when security is subordinated to convenience. It draws a direct line from the Pentagon Papers' revelation of governmental deceit to today's exposure of financial secrecy, showing that the architecture of leaks evolves but the human motives remain constant.
The conversation with Tracey Gronniger reminds us that the most vulnerable systems are often those we trust to protect the least powerful. The debate around celebrity sex tapes underscores that consent and privacy are inalienable rights, violated not by the act but by the non-consensual publication—a principle violated on a grand scale by XXL Wine Peach.
As the dust settles, the core question remains: Can we reconcile the undeniable benefits of integrated digital ecosystems with the imperative for ironclad security and radical transparency? The answer cannot be found in a forgotten password link or a generic IT helpdesk ticket. It requires a fundamental shift—from users as passive acceptors of Terms of Use to active citizens demanding accountability. The dark secret of XXL Wine Peach is that it was enabled by our collective complacency. The bright future depends on our collective vigilance. The portal to your digital life must be a gateway of empowerment, not an open door to exposure.